Technology Compliance Mistakes Businesses must avoid

Technology compliance ensures your business information technology remains current with industry standards and regulatory obligations.
Regulations governing information technology systems and company data are increasing significantly. IT professionals must adhere to these standards or face severe financial penalties for non-compliance.
When we introduce the phrase compliance, legal, compliance, and risk teams instantly become engaged. Below, we look at some common mistakes businesses make when pursuing compliance.
On this page:
Understanding Technology Compliance
CIOs and other top IT executives must understand the legislation around data, privacy, security, and other technology-related components. Regulatory standards are constantly changing, especially in IT security. Top executives can help avoid non-compliance and a hefty fine.
For example, IT personnel in the healthcare and related industries must comply with HIPAA, which safeguards electronic healthcare data, making the legal environment more complicated.
Why Information Technology Compliance is important
While maintaining compliance has always been critical, new technological advancements have heightened the need for more stringent IT compliance.
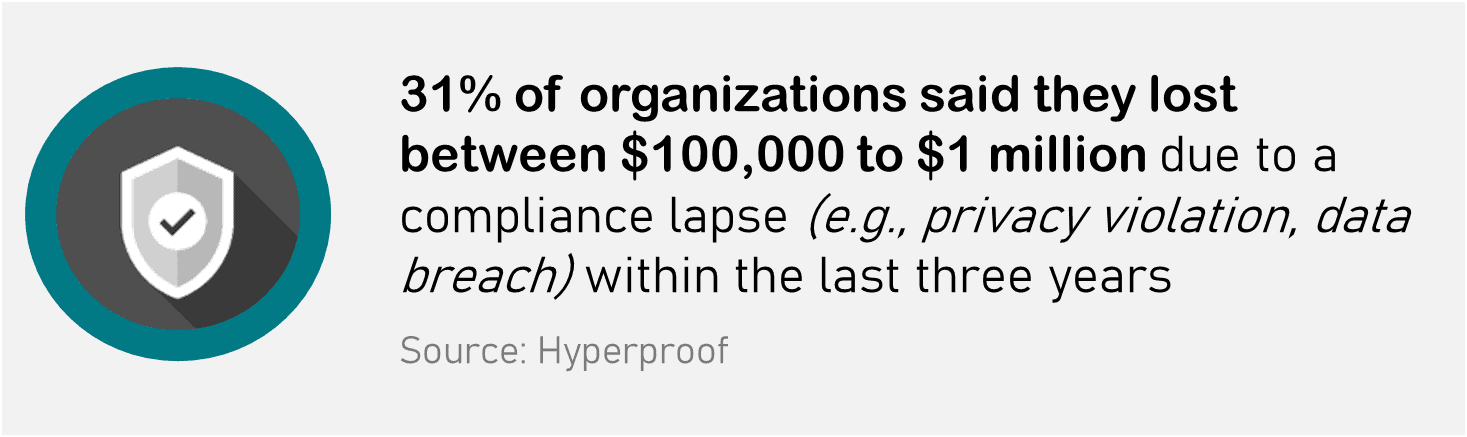
Failing to comply with standards may cost you millions of dollars in fines – it may also jeopardize the sensitive information of your customers and staff.
Four essential changes make compliance more difficult to maintain:
- Bring Your Own Device (BYOD) – Allowing staff to bring their gadgets to work might save you a lot of money. However, you also forfeit part of the essential supervision to be compliant without an adequately secure BYOD policy.
- Third-Party Vendor Management – Outside vendors assist you in running your business – you cannot do everything on your own, and suppliers may help you with several aspects of your business. However, moving data to a third-party provider might add risks, and several significant data breaches occur.
- Software Updates – Technology advances at a breakneck pace. As a result, software firms routinely offer new updates to address a vulnerability rather than introduce a nice new feature. Maintaining current software upgrades will keep your business secure and compliant.
- Internet of Things – IoT links intelligent gadgets, ranging from utilities to your home’s security system, as you come through the door. However, security in the IoT is behind, so you must regularly test devices for breaches or link them to a network that does not have access to essential data.
5 Compliance Laws Your Business needs to be aware of
Now that you understand why regulations are becoming more necessary and stringent, you’ll want to learn about the many IT compliance rules and how they apply to your firm.
The following are the top seven regulations that you should be familiar with:
1. The General Data Protection Regulation (GDPR) – Europe enacted GDPR in mid-2018 to assist enterprises in protecting consumer privacy.
- What Does It Do? The GDPR controls how businesses maintain personal data. It requires firms to map and catalogue their data across the enterprise, routinely audit their privacy compliance processes, and only access data when an individual has “opted in.” It compels all businesses to preserve records of data processing.
- What Industries Are Affected? Any industry that gathers, processes, or maintains personal data on European residents, EU enterprises, or European companies.
RELATED: Outline of the GDPR Data Protection Principles
2. PCI Data Security Standard (PCI-DSS) – The Payment Card Industry Security Standards Council comprises major payment card companies (i.e., Visa, American Express, MasterCard, Discover and JCB). PCI-DSS was developed in 2006 to maintain its security requirements.
- What Does It Do? PCI-DSS safeguards customer payment data. It consists of 12 rules aimed at reducing fraud, especially during transactions.
- What Industries Are Affected? Any organization that accepts, processes, saves or transmits credit card data.
RELATED: Understanding the Primary Goals of PCI DSS compliance
3. Health Insurance Portability and Accountability Act (HIPAA) – HIPAA was enacted in the US in 1996, with revisions and extensions throughout time.
- What Does It Do? HIPAA regulates how healthcare institutions handle electronic data and patient privacy. It also protects the healthcare of unemployed or laid-off workers.
- What Industries Are Affected? HIPAA impacts every company that deals with healthcare data, not only the healthcare industry. These are people who would have access to medical records for whatever purpose.
4. Sarbanes-Oxley (SOX) – The Sarbanes-Oxley Act was enacted to prevent another Enron or WorldCom. It became US legislation in 2002.
- What Does It Do? The Sarbanes Oxley Act requires financial records to be kept for seven years.
- What Industries Are Affected? Boards, management and public accounting firms of US public companies.
5. Gramm-Leach-Bliley Act (GLBA) – The GLBA, or Financial Services Modernization Act of 1999, allows commercial banks, investment banks, and insurance businesses to operate together. It also compels financial institutions to educate clients about data sharing.
- What Does It Do? The GLBA governs how financial institutions protect their customers’ and clients’ data.
- What Industries Are Affected? Financial institutions include companies that provide personal financial services such as investment advice, insurance, and loans.
5 Technology Compliance Mistakes to avoid
Any organization’s compliance and regulatory framework for information technology systems, networks, and hardware devices are integral to its operations.
Thus, CIOs must adhere to particular protocols and prevent errors resulting in non-compliance. They should avoid the following IT compliance errors:
1. Viewing your auditor as an opponent
When auditors and evaluators raise concerns about an organization’s IT projects and their impact on compliance, it’s natural for CIOs and other senior IT executives to become defensive.
These auditors will begin making observations about your cognitive process. This generates friction between the two, which is unproductive.
Thus, it is usually prudent to have a constructive and face-to-face talk, grasp the auditors’ perspective, and work together to improve the environment.
The essential truth is that everyone, even those who wrote these compliance requirements, is striving toward the same goal: establishing openness and accountability.
If CIOs embrace internal audits and work together with auditors, there is a good chance of simply resolving these compliance standards.
2. Mishandling exceptions
Just as every rule or guideline has certain exceptions, the IT framework likewise contains a set of compliance exceptions. Business conditions are more than likely to change, and consumer impact should be expected to evolve.
As a result, it is always advantageous to develop a procedure for managing IT compliance exceptions. It begins with simple documentation of what is being followed and why there may be a conflict with existing compliance.
Is the organization taking further measures to ensure compliance? Is the organization’s bypass rule permanent, or will it be subject to inspection and approval before implementation?
Businesses must ask such critical questions and document and monitor them consistently to avoid becoming hostile to or taking such exceptions for granted.
A thorough explanation should be provided whenever a regulation is disregarded, as such overlooked rules may pose a risk.
3. Failure of team readiness
As with other areas of information technology, even in the case of compliance, a lack of appropriate skills, experience, and necessary knowledge can result in serious difficulties. It is vital to have a prepared team to have a good strategy for IT compliance.
CIOs must guarantee that their teams constantly learn and develop to maintain IT regulatory compliance. Taking this strategy will significantly increase the efficiency of IT teams.
IT compliance is inextricably linked to the IT team; it is a cross-functional practice that makes it equally liable and accountable for every employee in the business, regardless of function.
4. Compliance controlling security
While it is critical to adhere to various Information Technology compliance requirements, most notably regulatory protocols, the goal should be to have a well-defined security methodology aligned with the organization’s business objectives and the vertical and domain in which the company or department operates.
When IT executives consider and align with this strategy, compliance becomes a clearly defined outcome rather than the sole objective.
Typically, core security measures are not managed efficiently but rather poorly, posing a compliance obstacle. Patching, vulnerability management, the use of two-factor authentication for remote access, the administration of mobile devices and BYOD policies are all instances of this category.
5. Unstructured Governance
Finally, while businesses may have established processes and implemented the necessary controls, they frequently overlook the governance structure and risk framework.
CIOs and other senior IT executives should develop a governance matrix that integrates enterprise systems, information security, and network/infrastructure teams to ensure that all Information Technology compliance requirements are met collectively.
That is the aspect determining success; its absence might be devastating.
Technology Compliance Goals and Challenges
The overarching purpose of information technology compliance is to provide a technological, procedural, and strategic framework that enables a business to achieve and demonstrate legal and ethical integrity.
By establishing secure methods, policies, and procedures, the following can be avoided:
- Deterioration of business image or customer trust
- Loss of revenue, stock value, or market potential
- Remediation costs (legal costs, fines, and judgments, purchased consumer protections, capital acquisitions, and lost productivity)
However, reaching this aim presents several obstacles, such as the intricacy and scope of newly enacted legislation are open to interpretation.
Due to the lack of a roadmap in the legislation, several industry-specific standards and best practices exist to give clarity and guidance.
Additional difficulties include the following:
- Inadequate staff education
- Shadow IT concerns, such as personal mobile devices that bypass corporate information technology systems
- Unauthorized software
- Difficulties with service providers (cloud computing and data centres)
- Existing and new regulations, updates, and laws
- The role of social media
Tips for Compliance Leaders
Compliances are rules meant to help businesses operate efficiently and ethically. Eliminating IT compliance issues is challenging, but organizations must constantly strive for compliance with regulatory standards.
As noted earlier, Information Technology compliance is a challenge. Several suggestions will help you avoid costly fines, penalties, and other legal ramifications:
- Educate staff on all areas of data privacy and provide them with protective measures
- Provide laptops and devices with security rules and preventative methods, such as remote wipe capabilities and safe access to business data, to mobile employees
- Implement authorization controls to restrict access to downloading programmes. Allow downloading of only approved software and apps
- Enforce encryption for security and prevent unauthorized access by devices
- Make use of only safe and cutting-edge cloud storage solutions
A robust information technology compliance framework enables you to:
- Ensure compliance with existing laws by integrating with data sources
- Standardize procedures across all applicable IT rules
- Increase effectiveness through automated processes and workflow
- Provide real-time IT compliance reports to leadership
- Maintain correct audit records
- Maximize investment in IT compliance services
- Integrate appropriate compliance best practices into procedures and workflows
- Manage IT resources effectively and assure responsibility
Finally, in today’s digitally connected environment, each employee must protect data and utilize equipment responsibly (laptops and computer use and safeguarding them even when off-site).
To protect the business in the case of an IT incident, better governance structures, rules and laws are required.

