Network Security 101: Network Firewall Best Practices all Businesses must follow
Most firewalls can provide some level of security straight out of the box. However, leaving your firewall to simply function according to faith won’t guarantee your business network security. To prevent malicious devices or software from accessing your network, firewall management best practices must be incorporated into your network security administration.
Hackers can quickly probe and identify businesses with a weak firewall system. Once identified, they can focus their efforts on breaching the company’s cyber defenses. To prevent malicious attacks, your firewall’s security must be frequently reviewed and optimized. All this will be covered as we identify network firewall best practices in the article below.
Before we get into the leading firewall best practices, let’s first review why firewalls are necessary and their importance to an organization’s cybersecurity posture.
On this page:
What is a Network Firewall, and How does it work?
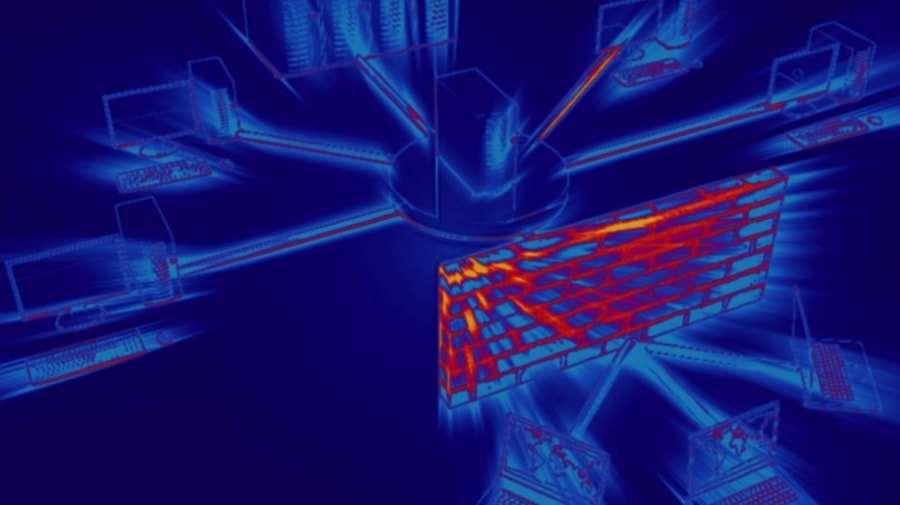
A network firewall is a security device and is an organization’s first line of defense against malware, viruses, and attackers attempting to access an organization’s internal network and systems maliciously.
RELATED: Types of malware businesses must protect against
Network security firewalls are implemented as hardware, software, or both, and monitor incoming and/or outgoing network traffic, blocking unauthorized data traffic based on predefined rules.
A firewall acts as a traffic controller or gatekeeper, creating a barrier between your business network and other networks such as the Internet. It helps protect your network and data by managing your network traffic, blocking unauthorized incoming network traffic, and validating access.
How does a Network Security Firewall work?
The data that comes into your business network is in the form of packets (a small unit of data). Each packet contains information about the source and destination. The intent of each data packet cannot be determined.
A firewall will only let connections that it has been set up to allow. It does this by permitting or blocking certain data packets based on IP addresses known to be safe. By determining the data packet’s source, i.e., the IP Address, firewalls filter and allow only legitimate traffic to enter your corporate network.
Most operating systems and security programs come with a firewall installed. It’s sensible to ensure these features are on and your security settings are set up so that updates run automatically.
Why does my Business need a Firewall?
Security and protection. Firewalls, along with corporate anti-virus software, form the cornerstone of any information security strategy.
Firewalls prevent unwelcome traffic from passing through. Firewalls stop external threats from reaching your network and prevent internal threats.
Here are some reasons why your business needs a network firewall:
- The first line of Defence from Unauthorised traffic: A firewall protects your corporate network from the Internet. External users can access your confidential corporate assets without a barrier. Business data and assets are in danger without a firewall. A firewall can protect you from hacking attempts, data breaches, and sometimes, DDoS attacks may even be prevented.
- Block access to Malicious Websites: A firewall can stop your users from going to certain websites outside of your network. It can also stop unauthorized users from getting into your network. For example, you could set up a rule that prevents your network from accessing social media sites like Facebook or YouTube.
- Protect Businesses from Malicious Code: Firewalls analyze incoming and outgoing network traffic and log infiltration attempts and policy infractions. Modern firewalls often include Data Loss Prevention (DLP) These features can detect sensitive data and prevent it from being leaked.
- Meter Bandwidth: A firewall does more than keep things safe. It can also measure and control the amount of network bandwidth that flows through it. For example, through QoS (Quality of Service), firewalls can limit the network bandwidth for non-business videos, music, and images. This lets you save bandwidth for business traffic which is more important.
- Provide VPN Services: Many firewalls can connect two sites through Virtual Private Network (VPN) services. This VPN feature allows mobile device users and remote sites to access your internal network resources safely. This makes it easier for people to work together and share information.
- Regulatory Compliance: Many data privacy/protection laws, regulations, and policies require firewall use either explicitly or implicitly. Examples include PCI DSS (the Payment Card Industry Data Security Standard), HIPPA (the Health Insurance Portability and Accountability Act), and GPDR (the General Data Protection Regulation). A firewall can help you increase your chances of meeting these regulatory mandates.
Types of Firewalls in Network Security
Structurally, firewalls can be software, hardware, or a combination:
- Software Firewall: A software firewall runs on computers and is usually included in operating systems and security programs, such as Avast Internet Total Security. Software firewalls prevent attacks from the outside, like unauthorized access, malicious attacks, and so forth, by warning when a harmful email is opened or when inadvertently accessing an insecure website.
- Hardware Firewall: A physical device that is placed at the network boundary. All network connections that cross this boundary go through this firewall. This lets it inspect incoming and outgoing network traffic and enforce access controls and other security policies.
RELATED: Software Firewall vs. Hardware Firewall: Which is Better?
There are also different kinds of firewalls based on how they work, and each kind can be set up as either software or a physical device. There are four different kinds of firewalls that work in different ways.
- Packet Filters: Also known as a static firewall, these firewalls control network access by watching outgoing and incoming packets and letting them through or stopping them based on the source and destination Internet Protocol (IP) addresses, protocols, and ports.
- Stateful Inspection Firewalls: Use dynamic packet filtering to control how data packets move through a firewall. These firewalls can check to see if a packet is part of a particular session. It will only allow communication if the session between the ends is perfectly set up. If it isn’t, it will block the communication.
- Application Layer Firewalls: These firewalls can look at information from the application layer of the OSI model, such as an HTTP request. If a suspicious application that could harm your network, or is not secure, is found, it is immediately blocked.
- Circuit-level gateways: A circuit-level gateway is a firewall that protects User Datagram Protocol (UDP) and Transmission Control Protocol (TCP) connections. It works between the transport and application layers of an Open Systems Interconnection (OSI) network model, such as the session layer.
What are Next-generation Firewalls (NGFW)?
Often referred to as intelligent firewalls, NGFWs accomplish the same tasks as the other types of firewalls mentioned already. However, they HoHHHalso incorporate extra features like application awareness and control, integrated intrusion prevention, and cloud-delivered threat intelligence.
5 Firewall Best practices to improve your Network Security
Your firewall’s effectiveness depends on the location of your firewall and its configuration. These are just a few of the factors that can affect your firewall.
1. Harden the Base Configuration
Block traffic by default, permitting only some specific traffic to certain known services, and monitor user access. Employing this approach allows you to control who has access to your network and prevent security breaches.
Firewalls are a business’s first line of defense against threats. It must be protected from all access.User permission control is required to ensure that only authorized administrators can modify firewall configurations.
A log must also be kept for compliance and audits whenever an administrator changes configuration.Unwarranted changes to the configuration can be detected, and configuration restoration may be performed in these cases.
Separate user profiles can be created to give different levels of access to IT staff. Firewall logs should be regularly monitored to detect any unauthorized break-ins of the firewall from outside or inside the network.
You can take security measures to protect your firewall and maintain its integrity. These are some firewall-hardening best practices that you can follow:
- Make sure your firewall software/firmware is up to date: This will ensure that no one can exploit your firewall’s vulnerabilities.
- Replace the default factory password: You can use a complex password that includes alphanumeric and non-alphanumeric characters and uppercase and lowercase characters.
- Use the principle of least privilege for firewall access: Only authorized administrators should be able to log in to make changes to your firewall.
- Do not use insecure protocols like HTTP, Telnet, and TFTP: It wouldn’t take long to get sensitive information (e.g., usernames and passwords) if someone intercepts the traffic.
2. Implement Firewall Change Control
Everyday there are changes that affect your IT infrastructure. New applications are installed, new network equipment deployed, user numbers increase, and non-traditional work methods may also be adopted. Your IT infrastructure’s attack surfaces will change as a result.
You shouldn’t take it lightly when making changes to your firewall. One simple error can cause some services to go offline, disrupting critical business processes. You could expose ports to the outside world and compromise their security.
You must have a plan for managing change before you make any changes to your firewall. The plan should outline the changes you are planning to make and the goals you have in mind. Your change control mechanism must contain anticipated risks and measures to mitigate them.
Keep track of all relevant information when you are creating your plan. When executing your plan, identify who made the changes and what they did. This will enable you to have an audit trail that you can refer back to if anything goes wrong.
After you have improved the performance of your firewall, it is time to ensure that it remains secure.
This plan will minimize the negative impact firewall changes can have on your business.
3. Plan and perform regular Firewall Security Audits
Companies have good reasons to perform compliance audits frequently. Companies typically conduct PCI DSS audits at least once per year. Compliance is generally only relevant for a specific time since there is no guarantee that a firewall device will always be compliant.
To identify policy violations, your IT security team, whether in-house or outsourced, should conduct regular and routine firewall security audits. The audits check whether firewall rules align with organizational security regulations or compliance requirements.
Unauthorized firewall policy changes could lead to non-compliance and expose your business to cyber threats.
An audit helps forecast how network changes may affect your security profile and should be performed every time you:
- Install a new firewall
- Conduct a firewall migration on the network
- Implement multiple firewall configuration changes
The following are standard firewall audits:
- Collect relevant information like previous audit reports, firewall/network Security Policies, network diagrams, and legitimate applications within your network.
- Ensure employees comply with firewall access control policies. This access should only be granted to authorized administrators.
- Checking firewall change management plans and making sure employees follow them. Reexamining your firewall monitoring process. Someone should monitor the firewall logs to detect potential threats and faulty rules.
- Review firewall rules and access control lists. Ascertain that they are still suitable for your current network setup.
To aid post-incident reporting or investigations, send your firewall logs to a security event management (SIEM) system.
Audits are also a way to ensure that firewalls you have acquired or migrated comply with your firewall policies. Combining your firewall configuration best practice with regular firewall security audits can be compliant and secure.
A firewall management plan was briefly mentioned earlier. Here are the details and reasons you should have it.
4. Optimize the Firewall Rules
For optimal protection, firewall rules must be well-defined and tuned. De-cluttering your firewall rule base can improve network security.
Your firewall rule base may include redundant components, duplication, or bloated superfluous rules that are ineffective. It’s vital to eliminate such rules to have more explicit guidelines. You can clean your firewall rule base by:
- Removing redundant rules or duplicate rules can slow down firewall performance. They cause the firewall to process more rules than necessary.
- You should remove rules that are no longer needed.They make firewall management much more complicated and threaten network security.
- Eliminate any shadowed rules which aren’t essential.These could lead to the neglect of more important rules.
- Disputes must be resolved.
- Any mistakes or inaccuracies must be corrected as they could lead to malfunctions.
If possible, use real-time monitoring to be alerted of any firewall changes.
5. Use a Centralized Management Tool for Multi-Vendor Firewalls
Multi-vendor firewalls can be found in many organizations.To provide additional security, companies prefer to have firewalls from different companies installed in their systems.The problem is that firewalls made by different companies have different architectures.
To ensure that all firewalls are working correctly, it is essential to have them all managed centrally.Multi-vendor firewall management tools allow you to view all firewall policies and rules in one place. This makes it easy to manage and compare firewall rules.
A centralized management tool will allow you to perform security audits and reports, troubleshoot configuration problems, and support firewall migration.
Firewall management is part of a broader Cybersecurity Strategy
Firewalls are an essential part of your business. However, just like other software devices, apps, and software, they require attention to work at their best and deliver results.
Poorly installed firewalls are worse than no firewall. This is also true for firewalls that have not been adequately planned or audited. These common mistakes in many businesses can lead to poor network security and a failed investment. However these mistakes can be avoided by adhering to the firewall best practices outlined above.
Firewalls are a significant investment for any business, ranging from $1,000 to more than $100,000. By following these firewall best practices, your can maximize your return on investment and increase the effectiveness of your firewall simply by using informed firewall practices.

