Sensitive Data Exposure: How is it different from a Data Breach?

People submit sensitive data into web apps every day, trusting the servers to safeguard their personal information against unwanted access. However, this is not always the case. Occasionally, these apps cannot guarantee proper protection, resulting in the exposure of sensitive data.
As the internet advances, so does data exposure. That is why it is to your best advantage to look for strategies to keep your sensitive data out of the wrong hands.
Below is the information you need to know about data exposure and data breach, allowing you to learn how to protect yourself.
On this page:
What is Sensitive Data Exposure?
Sensitive data is any piece of valuable information, mainly intended to be protected from unwanted access owing to its confidentially. Sensitive data includes bank account information, login credentials, phone numbers, credit card numbers, and social security numbers, among others.
See: 5 Essential data security best practices for keeping your data safe
That being stated, sensitive data exposure occurs when an individual or organisation unintentionally discloses personal data. In most cases, this might be caused by several circumstances, including a software fault, a lack of encryption, or data being uploaded to the incorrect database.
When hackers access this data, the owners’ sensitive information is revealed.
Your personal information can become public in two key ways—through sensitive data disclosure or a data breach. While these are often thought to be similar, they are not identical. Let us examine their distinctions.
Sensitive Data Exposure vs Data Breach: What is the difference?
When data or personal information stored on a server or database becomes available to undesired parties, this is referred to as data exposure. This occurs when the information of the system setup and web applications are not adequately safeguarded online.
Examples include keeping sensitive data in plain text and failing to protect websites using SSL and HTTPS protocols.
On the other side, a data breach happens when an individual’s information is accessed without consent. Malicious individuals intentionally cause data breaches, and firms with exposed data are the simplest and most frequent targets.
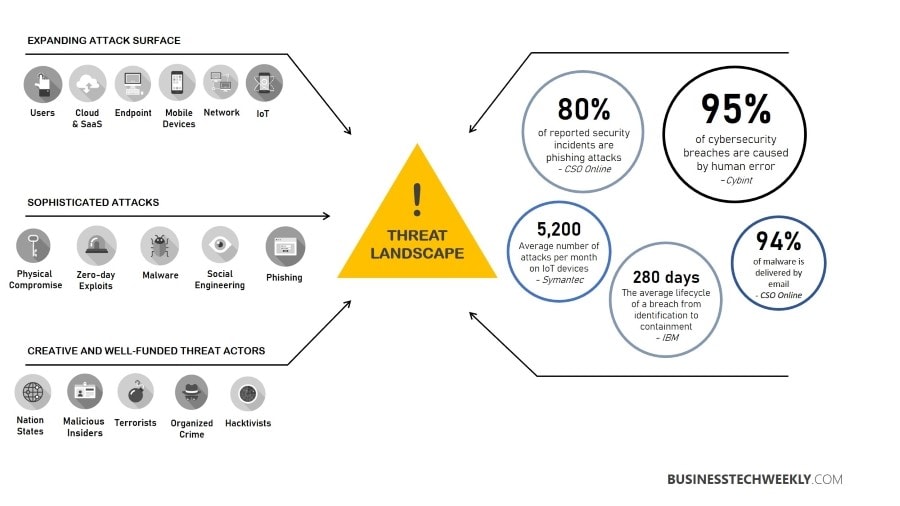
Hackers target programmes that have left sensitive user data exposed. Today, it is typical for sensitive data to be revealed. The security of many apps lags far behind the sophisticated tactics attackers use to exploit their flaws.
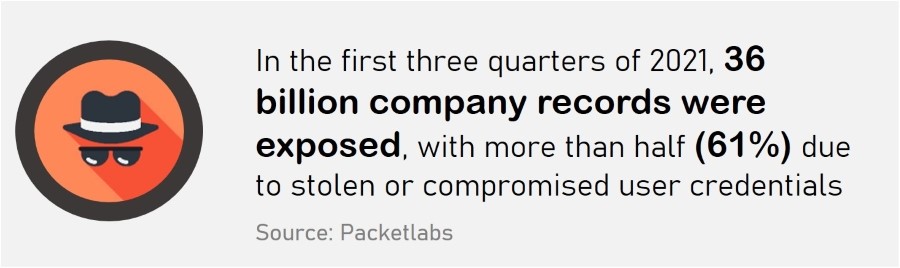
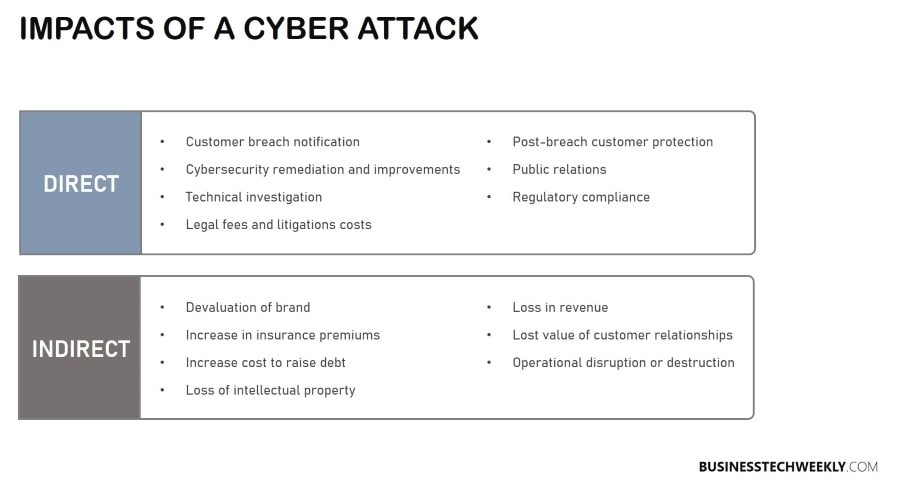
Even major corporations such as Yahoo! are not immune to assault. Between 2013 and 2014, they had one of the most significant data breaches in history, affecting over three billion users. This occurrence alone resulted in a loss of value for the organisation.
Numerous individuals risk losing money, personal information, and even their identities due to such attacks.
Why Web Applications are vulnerable to Data Exposure
Data isn’t static. Individuals initiate requests and commands, which are then transmitted over networks to other web servers, apps, and users. Data in transit can be hijacked, particularly when traveling over an unsecured network or between computer applications.
A form of eavesdropping, a Man-in-the-Middle (MITM) attack targets data in transit. The offender intercepts data in transit, puts themselves between the user and the programme, and then appears to participate in the data transmission.
Such assaults are primarily directed towards e-commerce websites, banking apps, SaaS enterprises, and other websites that require usernames and passwords.
Another method of compromising your data is through a system assault, which can occur on a server or a local computer. In this case, the data is stored on the system’s discs and is not in motion. You may believe that your internal data is secure, but this is not the case.
The reality is that hackers may access stored data via various routes, including Trojan Horse Malware. The virus obtains access to corporate data by convincing people to click on malicious links delivered through email or to download files from an infected USB stick.
Additional attack vectors for your online apps include the following.
1. Network Compromise
Individuals are in danger of having their data revealed if their network is breached. This can occur if attackers take control of users’ sessions—a technique is known as cookie hijacking.
A session is defined as when users are logged into an application. The exploitation of user ID sessions is then used to obtain unauthorised access to a service or information.
Numerous individuals have claimed identity theft due to a network breach incident. Their bank account information was exploited to make online transactions.
See also: Identity Theft: What to look out for
2. Structured Query Language (SQL) Injection Attacks
Structured Query Language (SQL) is a database programming language.
SQL injection attacks are the most common type of online application attack. They frequently occur against systems that include exploitable flaws. In a SQL attack, hackers make queries that execute malicious code.
If the servers lack the necessary security to detect altered codes, malicious actors can utilise the modified commands to access the sensitive data contained in the application.
Read: Software Application Security: Best Practices all Businesses must follow
3. Ransomware Attacks
Ransomware is software that thieves employ to encrypt personal and company data. Malware infects devices via malicious links or attachments that appear legitimate to users.
Once the URLs are visited, the ransomware is automatically downloaded and installed. It then encrypts and keeps files hostage. Before releasing the data, attackers want a ransom. Even after paying the ransom, the data is not disclosed in certain instances.
Related: Responding to a Ransomware Attack: The crucial initial steps businesses must take
How to Prevent Sensitive Data Exposure
While using online apps for one reason or another is the norm, it is still your job to safeguard against the disclosure of critical data. Here are some methods for securing your data.
1. Create Unique and Robust Passwords for your Accounts
With massive data breaches hitting the internet world, the very minimum you can do is create a strong password for each account you have online.
Cybercriminals are continuously on the lookout for security flaws, such as weak passwords, via which they may obtain access to your data.
You may create a secure and complicated password using capital, lowercase, symbols, and numbers. Additionally, avoid using the same password for many accounts. Rather than that, set a separate password for each account.
See also: 15 Tips for improving password security
2. Only access secure URLs
As previously noted, certain websites lack HTTPS security, putting them susceptible to data disclosure. These web apps are unsafe and should not be viewed, particularly if they require you to submit financial or personal information.
Secure websites begin with HTTPS://, whereas insecure websites start with HTTP://. Always keep an eye out for the “s” following the “p.”
3. Monitor your Financial Transactions regularly
Keep an eye out for strange behaviour in your bank accounts. Notify your bank immediately if you become aware of any to avoid a future breach.
You can also use your bank’s provisions to suspend or block your account if you suspect illegal activity.
4. Implement Effective Security Software
Security software is designed to safeguard users from the accidental disclosure of sensitive data online.
Ensure to install high-quality security software that covers virus and malware attacks. Also, make sure that you update your security software regularly. Failure to update it exposes you to cyber dangers.
Next Steps: Taking charge of your Sensitive Data
Connectivity to the internet has undoubtedly increased opportunities for both individuals and organisations. However, we also have the duty of safeguarding personal data when we engage in online interactions.
You do not have to live entirely off the grid out of fear of revealing your data. By understanding and executing self-protection methods, you can remain safe and secure in our online environment.

